A few weeks ago, on Oct. 1, 2016, Verisign successfully doubled the size of the cryptographic key that generates Domain Name System Security Extensions (DNSSEC) signatures for the internet’s DNS root zone. With this change, root zone Domain Name System (DNS) responses can be fully validated using 2048-bit RSA keys. This project involved work by numerous people within Verisign, as well as collaborations with the Internet Corporation for Assigned Names and Numbers (ICANN), Internet Assigned Numbers Authority (IANA) and National Telecommunications and Information Administration (NTIA).
As I mentioned in my previous blog post, the root zone originally used a 1024-bit RSA key for zone signing. In recent years the internet community transitioned away from keys of this size for SSL and there has been pressure to also move away from 1024-bit RSA keys for DNSSEC. Internally, we began discussing the root Zone Signing Key (ZSK) length increase in 2014. However, another important root zone change was looming on the horizon: changing the Key Signing Key (KSK).
In early 2015, ICANN assembled a design team tasked with making recommendations about changing the root zone KSK. As the design team wrapped up its work and delivered its report, it became clear that we could either work quickly to increase the ZSK in 2016 before the KSK rollover, or wait until some date in 2018 after the KSK rollover.
At the Root KSK Ceremony in May of this year, Verisign presented the first 2048-bit ZSK for signing, which was pre-published in the root zone on Sept. 20, 2016. Then, at the ceremony in August, we presented the next set of ZSKs to be signed, which will be used from October through December. On Oct. 1, 2016 we began publishing root zones signed with the larger ZSK.
A Look at the Data
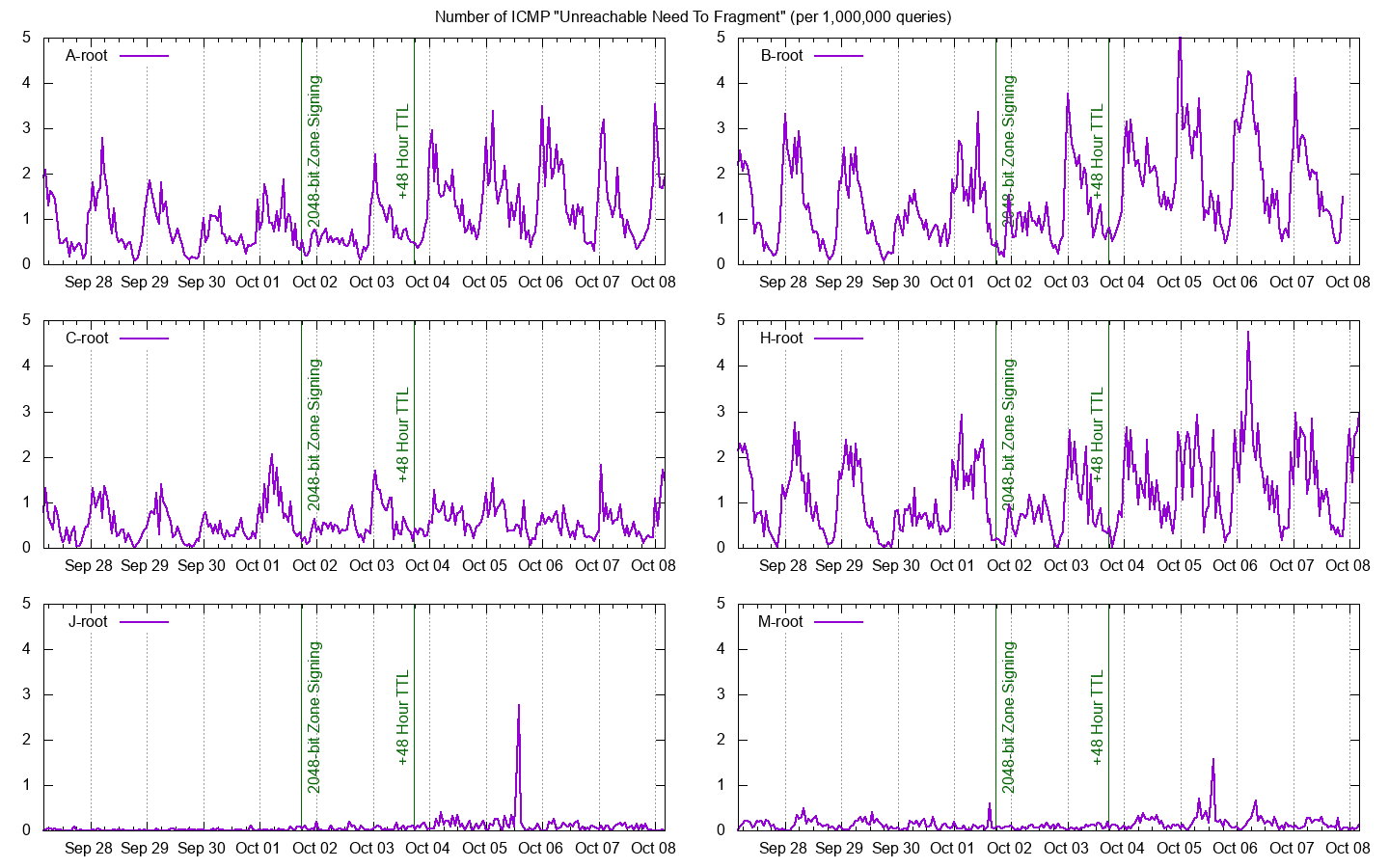
During these two important milestones we collected data with the assistance of our root server operator colleagues. With this data we can observe the rates of DNSKEY queries, UDP truncation, TCP-based queries, as well as ICMP “need to fragment” and “fragment reassembly time exceeded” signaling (see Figure 1). We’ve been closely watching this data for any evidence of problems related to the larger ZSK, and I’m happy to say that none has been found and no problems have been reported.
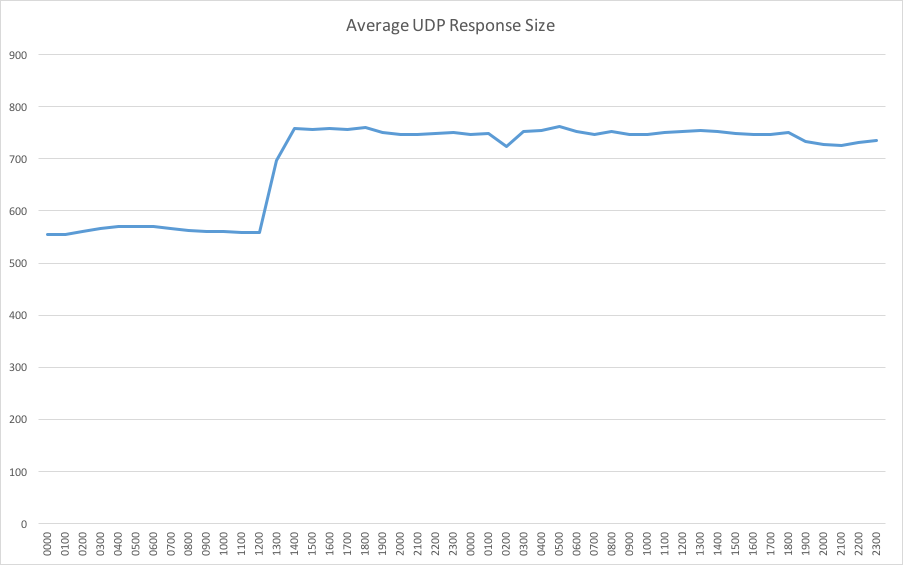
Apart from the increased level of security provided to internet users by the larger ZSK, the parties most affected by this change are the root operators. On Oct. 1, the size of the root zone file jumped from 1.6 to 2.1 MB. Furthermore, due to the high percentage of queries requesting DNSSEC records, all root servers experienced a sudden 30 percent increase in outgoing bandwidth (see Figure 2).
Thanks for a Smooth Implementation
I would again like to thank everyone who made this important change possible, especially those who we worked closely with at IANA (now Public Technical Identifiers), ICANN and NTIA. The root server operators played a crucial role and we appreciate their support and cooperation. Lastly, various DNS experts were also helpful in providing suggestions, criticisms and kudos throughout the process.
Although we feel confident that the ZSK length change occurred without any negative impacts, we encourage everyone to remain vigilant and report any potential issues to Verisign at info@verisign-grs.com.
On to the KSK Rollover…
Now that the ZSK length change is complete, we look forward to continued collaboration with ICANN on the KSK rollover. If you’ve had a chance to read their plans and documentation, you know that the KSK rollover timeline is longer and more complex, primarily because it involves updating trust anchors used by DNSSEC validators. We encourage everyone to follow this activity closely as it progresses during 2017.




