To establish connectivity with other users and devices, almost anything that interfaces with the internet depends on the accuracy, integrity and availability of the Domain Name System (DNS). Most online transactions and data movement are critically dependent on DNS services.
As such, DNS is an important point of security enforcement and a potential point in the Cyber Kill Chain for many cyber-attacks. Organizations are beginning to recognize this and are using DNS security mechanisms as a first line of defense for preventing or mitigating online threats.
Why DNS Is Important
DNS services are essential to the functioning of the internet. If an organization’s DNS services are down, the organization is effectively unreachable for most online purposes. That means data may be unable to enter—or leave—the organization’s network. Customers’ ability to do business with the organization could be interrupted, machine-to-machine interactions could come to a standstill, system synchronization may falter, application programming interfaces (APIs) might be impacted, and employees’ use of email or web collaboration tools to communicate could be disrupted.
Cybercriminals recognize the value of DNS availability and look for ways to compromise DNS uptime and the DNS servers that support it. According to a 2016 report, DNS was one of the most common services targeted by application-layer Distributed Denial of Service (DDoS) attacks, with more than 75 percent of respondents seeing such attacks. Any DNS downtime from attacks that either target DNS infrastructure or utilize it to launch other attacks can be extremely expensive. Costs may include, but are not limited to, potential reputational damage, customer churn, lost productivity, and remediation efforts. Revenue may also be impacted.
DNS Security Strategy is Essential
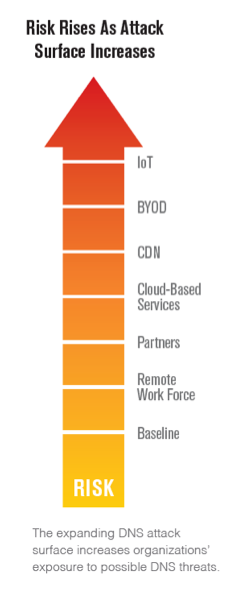
DNS, if not properly secured, may be susceptible to abuse by malicious actors. At the same time, the potential impact of a DNS attack is growing as organizations continue to rely more extensively on communication with partners, remote workers, cloud-based services, content delivery networks (CDNs) and more. The proliferation of mobile devices and the adoption of bring your own device (BYOD) strategies allow thousands of heterogeneous devices onto one network. If not properly managed, these devices can be used to introduce malware and advanced persistent threats. With the right planning and tools, DNS can be an effective part of the kill chain to disrupt these evolving attacks.
Another emerging trend is the internet of things (IoT). Gartner predicts that more than 20 billion “things” will be connected to the internet by 2020, with 7.2 billion of that total being used in businesses. As such, it is important for organizations to factor current and future IoT deployments into their overall DNS security strategy.
As DNS attacks grow in frequency and impact, organizations can no longer afford to overlook DNS security as part of their overall defense-in-depth strategy. As with IT security in general, no single tactic can address the entire DNS threat landscape or secure the complete DNS ecosystem. The key is to assess risks, identify security gaps, and develop a plan to strengthen the security of both your inbound and outbound DNS.
Considerations for Building a Framework for Resilient DNS Security
For more information on the importance of DNS in the security ecosystem, and considerations for securing DNS in your organization, download our free white paper, “Framework for Resilient DNS Security.”
Verisign Security Services offers cloud-based DDoS protection and DNS solutions to protect your online services from today’s security threats. Click here for more information about Verisign Security Services.




1 comment
Comments are closed.