This is the first in a multi-part blog series on cryptography and the Domain Name System (DNS).
As one of the earliest protocols in the internet, the DNS emerged in an era in which today’s global network was still an experiment. Security was not a primary consideration then, and the design of the DNS, like other parts of the internet of the day, did not have cryptography built in.
Today, cryptography is part of almost every protocol, including the DNS. And from a cryptographer’s perspective, as I described in my talk at last year’s International Cryptographic Module Conference (ICMC20), there’s so much more to the story than just encryption.
Where It All Began: DNSSEC
The first broad-scale deployment of cryptography in the DNS was not for confidentiality but for data integrity, through the Domain Name System Security Extensions (DNSSEC), introduced in 2005.
The story begins with the usual occurrence that happens millions of times a second around the world: a client asks a DNS resolver a query like “What is example.com’s Internet Protocol (IP) address?” The resolver in this case answers: “example.com’s IP address is 93.184.216.34”. (This is the correct answer.)
If the resolver doesn’t already know the answer to the request, then the process to find the answer goes something like this:
- With qname minimization, when the resolver receives this request, it starts by asking a related question to one of the DNS’s 13 root servers, such as the A and J root servers operated by Verisign: “Where is the name server for the .com top-level domain (TLD)?”
- The root server refers the resolver to the .com TLD server.
- The resolver asks the TLD server, “Where is the name server for the example.com second-level domain (SLD)?”
- The TLD server then refers the resolver to the example.com server.
- Finally, the resolver asks the SLD server, “What is example.com’s IP address?” and receives an answer: “93.184.216.34”.
Digital Signatures
But how does the resolver know that the answer it ultimately receives is correct? The process defined by DNSSEC follows the same “delegation” model from root to TLD to SLD as I’ve described above.
Indeed, DNSSEC provides a way for the resolver to check that the answer is correct by validating a chain of digital signatures, by examining digital signatures at each level of the DNS hierarchy (or technically, at each “zone” in the delegation process). These digital signatures are generated using public key cryptography, a well-understood process that involves encryption using key pairs, one public and one private.
In a typical DNSSEC deployment, there are two active public keys per zone: a Key Signing Key (KSK) public key and a Zone Signing Key (ZSK) public key. (The reason for having two keys is so that one key can be changed locally, without the other key being changed.)
The responses returned to the resolver include digital signatures generated by either the corresponding KSK private key or the corresponding ZSK private key.
Using mathematical operations, the resolver checks all the digital signatures it receives in association with a given query. If they are valid, the resolver returns the “Digital Signature Validated” indicator to the client that initiated the query.
Trust Chains
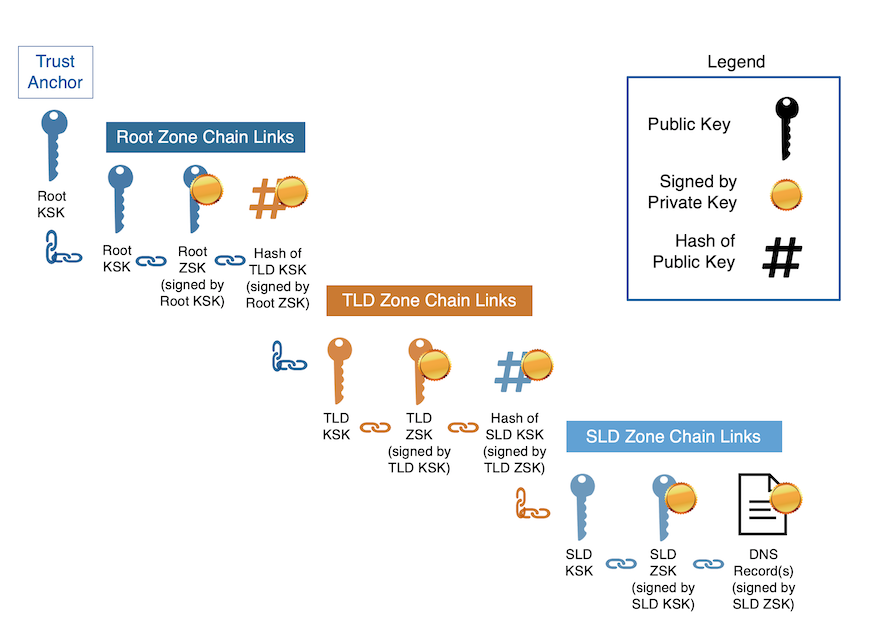
A convenient way to visualize the collection of digital signatures is as a “trust chain” from a “trust anchor” to the DNS record of interest, as shown in the figure above. The chain includes “chain links” at each level of the DNS hierarchy. Here’s how the “chain links” work:
The root KSK public key is the “trust anchor.” This key is widely distributed in resolvers so that they can independently authenticate digital signatures on records in the root zone, and thus authenticate everything else in the chain.
The root zone chain links consist of three parts:
- The root KSK public key is published as a DNS record in the root zone. It must match the trust anchor.
- The root ZSK public key is also published as a DNS record. It is signed by the root KSK private key, thus linking the two keys together.
- The hash of the TLD KSK public key is published as a DNS record. It is signed by the root ZSK private key, further extending the chain.
The TLD zone chain links also consist of three parts:
- The TLD KSK public key is published as a DNS record; its hash must match the hash published in the root zone.
- The TLD ZSK public key is published as a DNS record, which is signed by the TLD KSK private key.
- The hash of the SLD KSK public key is published as a DNS record. It is signed by the TLD ZSK private key.
The SLD zone chain links once more consist of three parts:
- The SLD KSK public key is published as a DNS record. Its hash, as expected, must match the hash published in the TLD zone.
- The SLD ZSK public key is published as a DNS record signed by the SLD KSK private key.
- A set of DNS records – the ultimate response to the query – is signed by the SLD ZSK private key.
A resolver (or anyone else) can thereby verify the signature on any set of DNS records given the chain of public keys leading up to the trust anchor.
Note that this is a simplified view, and there are other details in practice. For instance, the various KSK public keys are also signed by their own private KSK, but I’ve omitted these signatures for brevity. The DNSViz tool provides a very nice interactive interface for browsing DNSSEC trust chains in detail, including the trust chain for example.com discussed here.
Updating the Root KSK Public Key
The effort to update the root KSK public key, the aforementioned “trust anchor” was one of the challenging and successful projects by the DNS community over the past couple of years. This initiative – the so-called “root KSK rollover” – was challenging because there was no easy way to determine whether resolvers actually had been updated to use the latest root KSK — remember that cryptography and security was added on rather than built into the DNS. There are many resolvers that needed to be updated, each independently managed.
The research paper “Roll, Roll, Roll your Root: A Comprehensive Analysis of the First Ever DNSSEC Root KSK Rollover” details the process of updating the root KSK. The paper, co-authored by Verisign researchers and external colleagues, received the distinguished paper award at the 2019 Internet Measurement Conference.
Final Thoughts
I’ve focused here on how a resolver validates correctness when the response to a query has a “positive” answer — i.e., when the DNS record exists. Checking correctness when the answer doesn’t exist gets even more interesting from a cryptographer’s perspective. I’ll cover this topic in my next post.
Read the complete six blog series:
- The Domain Name System: A Cryptographer’s Perspective
- Cryptographic Tools for Non-Existence in the Domain Name System: NSEC and NSEC3
- Newer Cryptographic Advances for the Domain Name System: NSEC5 and Tokenized Queries
- Securing the DNS in a Post-Quantum World: New DNSSEC Algorithms on the Horizon
- Securing the DNS in a Post-Quantum World: Hash-Based Signatures and Synthesized Zone Signing Keys
- Information Protection for the Domain Name System: Encryption and Minimization




